Governance & Architecture
Technical overview of Echo Health's multi-tenant isolation, access control enforcement, audit logging, and operational safeguards.
Governance-First Platform Design
Access control and data isolation are enforced at the API Gateway layer before any request reaches downstream services.
Tenant isolation is enforced at the API Gateway layer. Every request must include a valid tenant identifier. Requests without tenant context are rejected before reaching any downstream service.
All data access requires the following validations to pass:
- Authenticated identity: Valid JWT with verified signature and unexpired session
- Tenant validation: Request tenant matches authenticated user's tenant assignment
- Role-based authorization: User role permits the requested operation on the target resource
- Purpose-of-use validation: Request purpose header is present and valid for the data category
Consent records are versioned. Each consent grant or revocation creates an immutable record with timestamp, grantor identity, and scope. Consent state is evaluated at request time.
- All access attempts are logged, including successful and denied requests
- Administrative actions are immutably logged with actor identity and timestamp
- Audit events are queryable per tenant for compliance review and incident response
High-Level Architecture Overview
System architecture diagram showing request flow, authentication, and service boundaries.
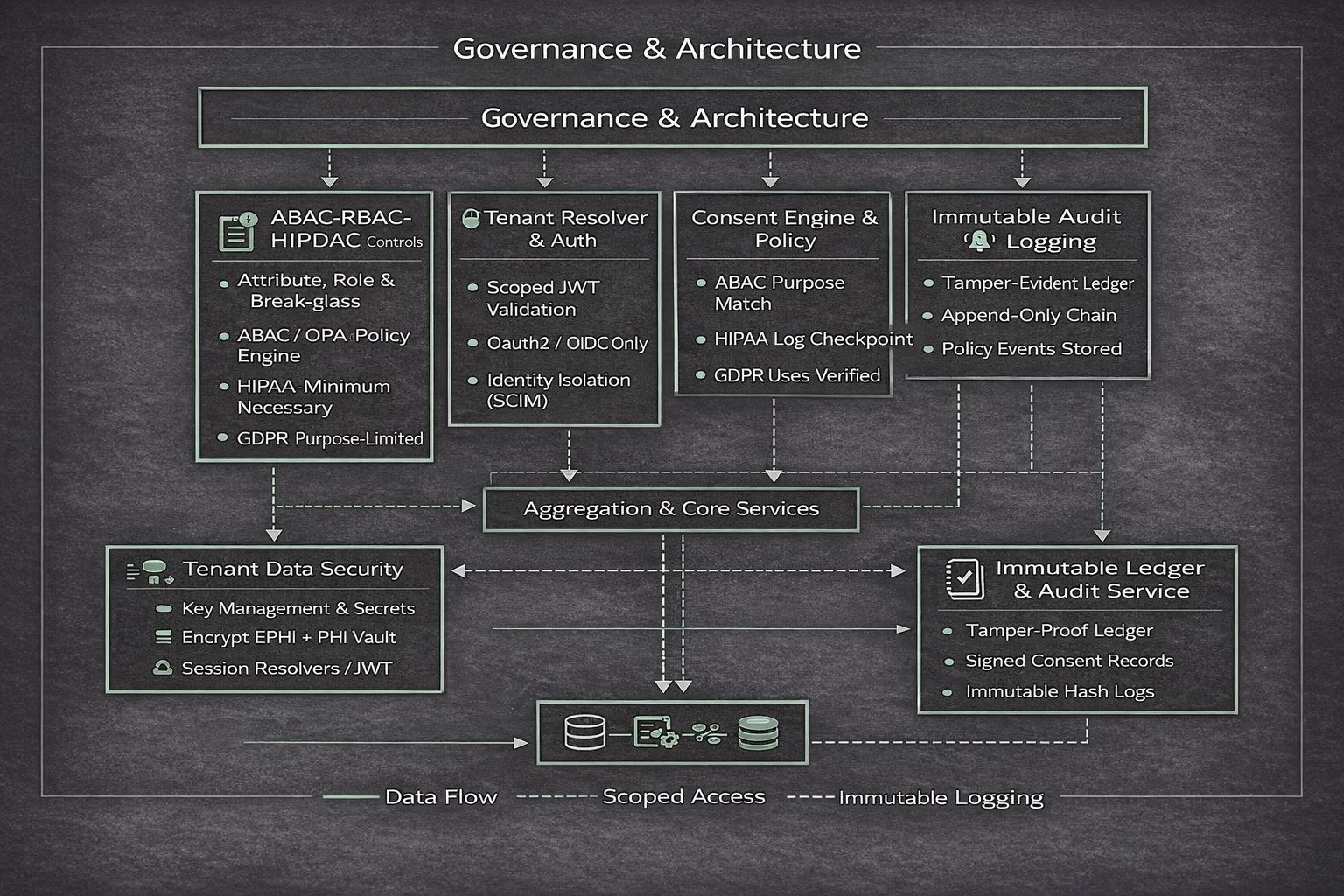
- Multi-tenant logical isolation at gateway and data layers
- JWT-based identity validation with signature verification
- Role-Based Access Control (RBAC) with tenant-scoped permissions
- TLS 1.3 encryption for all data in transit
- AES-256 encryption for data at rest
- Immutable audit logging for all enforcement decisions
- Structured observability: metrics, logs, and alerting
Operational Safeguards
Runtime controls and operational boundaries enforced in production.
Feature flags control pilot scope. Features can be enabled or disabled per tenant without deployment. Flag state changes are logged.
API rate limits and request quotas are enforced at the gateway. Limits apply per tenant and per endpoint category.
AI assistance is bounded to non-clinical scope. AI does not make clinical decisions, prescribe, diagnose, or override clinician judgment.
Manual override and human escalation pathways are available. Critical workflows include explicit escalation triggers to human reviewers.
Disaster recovery procedures are documented and tested. Backup and restoration processes are validated. RTO and RPO targets are defined per service tier.
Security and Compliance Inquiries
For security documentation, compliance questionnaires, or technical architecture questions, contact the security team.